Politics may make for strange bedfellows, but there’s no comparison to the match-ups that occur in the business world. Consider this: Mozilla, which has been flexing its muscles of late and pushing into the smartphone business and foreign markets, announced on Wednesday that it has teamed up with the flailing and failing BlackBerry, which is hemorrhaging market share, to conduct research on bugs in browsers.
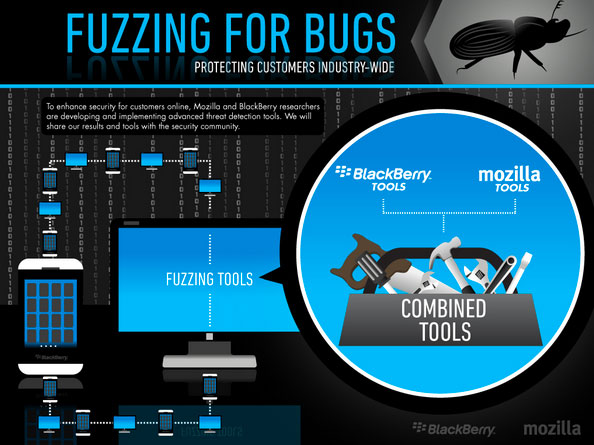
The two will expand their collaboration on advanced automated security techniques known as “fuzzing.”
Perhaps their teaming up is not as strange as it might first appear.
“Very often, security partnerships are the result of professionals discussing an idea at a conference,” remarked Randy Abrams, a research director at NSS Labs. “I would expect [the collaboration] has to do with like-minded people discussing an idea and saying ‘we can do this.'”
BlackBerry “has always been into browsers,” Maribel Lopez, principal at Lopez Research, told LinuxInsider. “They were doing the Webkit thing pretty early and trying to build another browsing experience.”
Making the World Safe
The two partners will focus on fault injection. This involves providing invalid, unexpected or random data to the inputs of a computer program and monitoring it for crashes, memory leaks and other problems.
Fault injection lets security researchers identify potential weaknesses so they can be dealt with before they become a threat to users.
Mozilla and BlackBerry will work with the open source fuzzing Peach v2 framework.
Feeling the Fuzz
Fuzzing can be used on any type of program input, and it can be extended to the contents of databases or shared memory. It can indicate which parts of a program require special attention such as a code audit or rewrite.
Fuzz testing offers a high benefit-to-cost ratio, but passing a fuzz test is not definitive proof that a program is functioning correctly. It may only show that a program can handle exceptions without crashing.
Security experts also use fuzz testing to find bugs such as assertion failures — and when coupled with a memory debugger, to locate memory leaks.
Biting Into Peach
There are two forms of fuzzing: mutation-based and generation-based. The first mutates existing data samples to create test data, and the second defines new test data based on models of the input. Peach can perform both.
Users have to first create PeachPit files to define the structure, type information, and relationships in the data to be fuzzed. Peach lets users configure a fuzzing run, including selecting a data transport and logging interface.
Peach has been under active development since 2004, and version 3 Release Candidate 1 was recently launched.
Mozilla has used Peach to help secure Firefox and Firefox OS.
BlackBerry and Open Source
BlackBerry has used large-scale automated testing for years to identify security issues in its platform. It uses its own proprietary fuzzing tool as well as third-party fuzzers.
The company’s collaboration with Mozilla plugs directly into its existing security processes and infrastructure, and it has worked with Mozilla on fuzzing activities before.
BlackBerry embraced open source when it signed on to Github in 2010. It also went open source with the QNX operating system, which powers BB 10.
Bringing Up Minion
Mozilla on Wednesday also launched Minion, a free, open source security testing platform for developers and security professionals to scan and test websites and services.
Minion focuses on correct and actionable results that do not need validation by a security professional. It has three major components — plugins, a task engine and a front end.
The platform is designed so any developer can use it, regardless of security expertise.
“I don’t think either Mozilla or BlackBerry are promising perfect security,” NSS Labs’ Abrams told LinuxInsider.
“Mistakes are bad, but if more problems are fixed than mistakes are allowed past, the net result is improved security,” he pointed out.
“Amputating the wrong limb is really bad,” Abrams continued,” but having no medical treatment at all for anyone is even worse.”