
![]()
Qubes OS is a hybrid computing technology that raises the bar for security. It takes locking down computers to a new level.It has advanced far beyond the primitive proof of concept demonstrated more than four years ago. Release 2 (beta), which arrived in late September, is a powerful desktop OS.
Qubes succeeds in seamless integrating security by isolation into the user experience. However, comparing Qubes to a typical Linux distro is akin to comparing the Linux OS to Unix.
Qubes is more a Xen distribution than a Linux one — but Qubes is much more than just Xen packaging. It has its own VM management infrastructure, with support for template VMs and centralized VM updating. It also has a very unique GUI virtualization infrastructure.
If you are looking for an out-of-the-box fun operating system for casual use, look elsewhere. Qubes OS is hard-core security with little in the way of eye candy.
What It Is
Qubes is a security-oriented OS designed to provide strong security through isolation. It is a hybrid that is built upon Xen, X Windows and Fedora Core 18.
Given this unusual mixture of platforms, it is not accurate to think of Qubes as a Linux distro. Qubes uses the Linux kernel and platform as an application programming interface for apps and drivers.
This hybrid OS uses the underbelly of Linux and its flexibility to coexist in a Xen-like environment.
It’s like using a VMware server with multiple guest OSes, explained Joanna Rutkowska, founder and CEO of Invisible Things Lab.
Each component runs in the equivalent of its own virtual machine. This creates an isolation from each running element. Each OS has a separate purpose. For instance, you do casual Web browsing in one system. You do sensitive work correspondence or spreadsheet tasks in another.
The real usefulness of Qubes from a security standpoint is the isolation factor. For instance, you can create a component that has no network access to store highly sensitive data.
How It Works
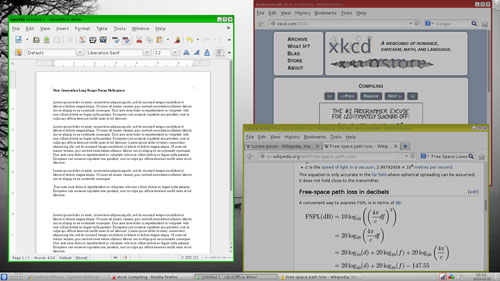
Unlike locating each task in a true separate virtual machine running on the same hard drive, Qubes OS runs each separate component in its own window environment on the same screen. In essence, you can view and use each active “window” much like you would maintain open windows on the same desktop.
Dom0 is the admin domain of the Qubes OS. “Dom0,” short for “domain zero,” is the initial domain started by the Xen hypervisor on boot.
The components of the operating system and the user workspaces are isolated into functional domains. The idea behind this isolation of computing components is that if one component is compromised, the entire system and your data are not vulnerable.
Installing Qubes
The first thing to do is check if your computer supports hardware virtualization technologies. You can install Qubes without VT support, but you will get better performance and security with it.
Intel and AMD added extensions to support virtualization in their processors. A quick check of your system’s specs will identify that support as Intel VT-x and AMD-V.
Even if you have a system with the extensions, you might have to enable the support. Check the BIOS settings.
Perhaps a bigger stumbling block is the need to actually install Qubes on your hard drive. The ISO does not support live session.
A key system requirement is memory. Qubes needs at least 4 GB of RAM for good performance. The developers note that you can make it work with 2 GB. However, minimal RAM will impact Qubes’ performance.
Decide which flavor you wish to install. This choice comes early in the process when you boot the computer. Remember, the ISO file does not first load into a live session from which you select the Install option.
Instead, the opening screen prompts you to select a language for running Qubes. The usual hard disk options exist in terms of installing over the existing data or running GParted functions to create a new partition for Qubes.
You also select KDE, Xfce or both desktop environments. This seems a bit foolish, as the default triggers the installation of both KDE and Xfce. So unless you have a preference for the desktop shell, you can put off that running decision until you start using Qubes.
Using It
As part of your first launch of Qubes, be sure to update the TemplateVM. This will apply the latest security patches. You do this in a terminal session. The two commands are yum check-update and yum update.
As with a full-fledged Linux distro, you can manipulate to a degree the way the interface works. You do this by clicking the menu icon at the far left end of the panel. The System Settings options in either environment should be familiar. The Xfce or KDE desktop options let you set up the user interface your way, at least to an extent.

Also be sure to configure your domains. Remember that in Qubes, domains are the settings for each component you run in its own window.
Open the TemplateVM and use yum to install new software. Use the AppVMs to add to the list of applications listed in that AppVM menu.
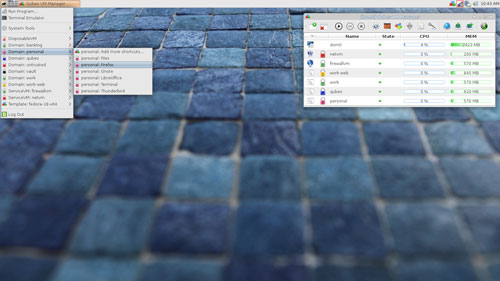
Each domain window displays with a color code. Each domain has its own set of security properties. These color cues makes it easy to recognize the concept of compartmentalized security at work.
Not Pure Linux
As I played around with Qubes, I realized that a working knowledge of the Fedora Linux distro makes it much easier to use. Using the yum command structure is one case in point.
However, Qubes has its own architecture, so expect a learning curve and ample sessions devoted to reading the documentation. For instance, you need to learn the command line structure required to create domains.
The component windows is another area that needs getting used to. You can run an application in an existing AppVM, but the settings and data will be gone when you close the VM window. To keep that app and its settings and data persistent, you must create a standalone VM and then install the software in that component.
Another difference is sharing text among component windows. The copy-and-paste process is a bit different. For example, in the application running in the source domain, first copy the text using ctrl+c. Then press ctrl+shift+c. Next, select the application in the destination domain and press ctrl+shift+v and then press ctrl+v.
Bottom Line
The concept behind the Qubes OS is a security by compartmentalization approach. It can run most Linux applications and utilize most of the Linux drivers. Qubes is developed in the U.S. for x86_64 architecture.
If security is a primary requirement for your computer system, Qubes OS offers a unique solution. It is not the same as using virtualization to run an entire operating system.
Want to Suggest a Review?
Is there a Linux software application or distro you’d like to suggest for review? Something you love or would like to get to know?
Please email your ideas to me, and I’ll consider them for a future Linux Picks and Pans column.
And use the Talkback feature below to add your comments!





















































Qubes announced a partnership with Purism today to preinstall Qubes OS on Librem notebooks. Runs perfectly on the hardware. The companies intend to focus on developing a more secure and easier to use OS and laptop in the future.