The open-source Android operating system has long been considered by security experts to be the mobile OS most vulnerable to security threats, but iOS is just as vulnerable, Marble Security has found.
However, the two OSes expose users to different types of threats.
The perceived greater security of iOS rests on Apple’s control of app distribution rather than on any inherent superiority of the OS over Android, Marble said.
Marble analyzed the vulnerability of 12 million Android and iOS apps to 14 leading mobile security threats.
The finding is both good and bad news, Marble founder and CTO Dave Jevans told LinuxInsider.
“The good news is, more mobile devices are being managed by businesses,” Jevans explained. “The bad news is, both major platforms expose corporate networks because they are designed to communicate, and users can install risky apps unknowingly.”
What Else Marble Discovered
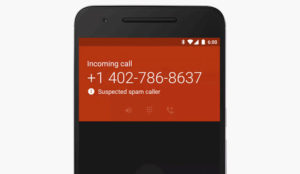
The attack surfaces of Android and iOS are not too different, and attackers have found ways to publish malicious apps or to attack mobile users over SMS or through compromised WiFi hotspots on both, Marble found.
Rooting Android devices is no riskier than jailbreaking iOS devices — which Apple frowns upon and which negates device warranties.
Both Android and iOS apps routinely require risky permissions such as the right to read contacts, email messages, and text messages. Once that data is uploaded to the app provider, it is no longer controlled by the mobile device — or, in a BYOD situation, the enterprise. That represents a significant potential threat to security, Marble said.
Hackers can use jailbreak jammers to prevent mobile device management programs from detecting that a device has been rooted or jailbroken, Jevans noted.
Both Android and iOS are vulnerable to address book harvesting attacks, which allow very convincing spearphishing attacks, he said.
Diff’rent Strokes
Still, the threats users face differ between the platforms.
“Android is more vulnerable to harvesting phone call logs and SMS logs and sideloading apps,” Jevans pointed out. “iOS is more vulnerable to hostile MDM configuration profiles.”
Overall, the enterprise is at risk for intercepted traffic, fake app installation, sophisticated phishing, and advanced persistent threats, he continued.
It’s the Wetware, not the Technology
“For years, iOS, like the Mac, got by on security via obscurity,” Laura DiDio, principal at ITIC, told LinuxInsider, “but the biggest issue in security is user behavior.”
A mobile security survey ITIC conducted in April found that human error is the biggest threat, she said.
“Forget about the security of the devices when you have humans sitting in public places giving their credit card numbers out loud to make purchases over the phone, or not blocking their devices when they’re using them in public places because it’s too much trouble,” DiDio said.
Further, 35 percent of the more than 600 survey respondents said they had no idea or way of knowing if their employee-owned BYOD devices had been hacked or compromised, but 70 percent were “pretty confident” in the security of their BYOD devices, DiDio revealed.
Fun and Games May Hurt
Gaming and news apps on iOS devices present “significantly greater” security risks than other app categories, Marble discovered.
Things might get worse soon — Facebook has begun rolling out an iPad app update that would make it a hub for game, video, and content discovery.
How Enterprises Might Cope
Businesses with a BYOD policy might ban apps based on the risk they pose to the enterprise, Marble’s Jevans suggested. This should be based on the app’s code and how it communicates, what data it communicates, and whom it communicates that data to.
Alternatively, policies can restrict access to enterprise network resources from devices that have risky apps, Jevans mooted.
“Our survey found that most companies don’t have a security policy,” DiDio pointed out.
Another option: Switch to BlackBerry, which has a far more secure OS than any other vendor — but, as Jevans said, “that’s not gonna happen.”