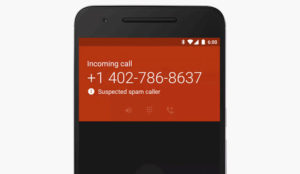
Google has begun rolling out a patch to fix a security flaw in versions 2.3.3 and earlier of its Android mobile operating system.
That flaw affects all Google services using the ClientLogin authentication protocol.
It lets hackers access any personal data available through Android’s application programming interfaces (APIs).
“The flaw is now fixed for all versions of Android worldwide,” Google spokesperson Randall Sarafa told LinuxInsider.
The patch is being rolled out in stages over several days, Sarafa said.
The Hole in Android
The flaw gained media attention after it was publicized by the University of Ulm.
Here’s how it works: When an application wants to get access to Android’s APIs, it requests an authentication token through ClientLogin by providing an account name and password.
The system then returns an authorization token, which is good for up to two weeks.
If the token is used in requests sent over unencrypted networks, such as WiFi networks, hackers can steal it. They can then use the token to access any personal data made available through the service API.
The hackers will gain full access to the victim’s calendar, contacts information, or private Web-based photo albums. They’ll be able to view, delete, or modify any calendar events, contacts, or private pictures, the Ulm University researchers said.
The flaw affected 99.7 percent of all Android smartphones running Android 2.3.3 and earlier versions because they don’t use a secure HTTPS connection, the researchers said.
Google’s patch forces an HTTPS connection for calendar and contacts sync on Android, Sarafa said.
More on the Flaw
Authentication tokens are widely used for online services such as eBay. They are also used by software and application vendors such as Microsoft and Splunk, and in Apple’s iOS mobile operating system.
There was a problem with the authentication token on Android because Google’s implementation was faulty, Paul Laudanski, director of ESET’s cyber threat analysis center, told LinuxInsider.
“The entry point is having an unpatched or vulnerable Android system connecting to Google services using ClientAuth over an unencrypted public WiFi network,” Laudanski explained. “The correct implementation is to transmit the authorization token in a secured manner.”
Google services transmit the authorization token as an open text message, which can be easily stolen.
If the technology is implemented correctly and the authorization tokens are sent securely, then even if an unencrypted WiFi network is used, the user information would appear as garbage to snoopers, Laudanski pointed out.
Google’s implementation of the technology may not have been faulty in and of itself, argues Mike Paquette, chief strategy officer at Top Layer Security.
“The problem appears to be the use of the ClientLogin protocol, allowing these sniffable authentication protocols, combined with a long expiry time,” Paquette told LinuxInsider. “This makes exploits practical and even likely,” he added.
Android smartphone owners should stay away from heavily used public WiFi hotspots, Paquette warned. “It’s likely that attackers would target areas with large numbers of users of public WiFi in order to have the greatest return,” he explained.
Old Problems Refreshed
The security flaw in Android was apparently first discovered by Dan Wallach of Princeton University, who blogged about it in February.
In an experiment during his undergraduate security class, he set up a sniffer with fellow students to listen in on his Android smartphone. They used Wireshark and Mallory.
Wireshark is a network protocol analyzer for Unix and Windows. Mallory is a transparent TCP and UDP proxy. It can be used to access network streams and assess mobile Web applications, among other things.
UDP, the User Datagram Protocol, is one of the core members of the Internet Protocol (IP) Suite. It lets applications directly send messages, or datagrams, to other hosts on an IP network.
The team found that Google doesn’t encrypt traffic to Google Calendar, although it properly encrypts traffic to Gmail and Google Voice. Eavesdroppers could see victims’ calendar transactions and likely impersonate them on Google Calendar, Wallach found.
The University of Ulm researchers built on Wallach’s research.
Android smartphone users should apply the same security precautions to their devices as they would do with their laptops, Torsten George, vice president of marketing at Agiliance, told LinuxInsider.
“Smartphones are essentially taking on the role of a regular computer,” George pointed out. “Thus, they are just as vulnerable to attack by cybercriminals as regular laptop or desktop computers.”
Because they lack built-in security, smartphones “open up a bigger attack surface than traditional computer devices,” George added.